Picture this: a key employee resigns. A few weeks later, your customers receive outreach from a competitor; pricing suddenly gets undercut, and internal processes start appearing elsewhere.
That “walk-out-the-door” moment is one of the most common, and costly, risks facing growing businesses in San Antonio and across Texas.
In 2026, protecting your business information is all about proving that you treated your information like a trade secret in the first place.
Courts protect information that is both valuable and actively guarded. The difference matters most when an employee leaves.
Let’s walk through what counts as a trade secret, where businesses lose protection, and what actually works when you need to move fast.
Why Trade Secret Protection Matters More in 2026
Employee mobility is higher than ever, and copying business information is faster and harder to detect.
The regulatory environment has also shifted. The Federal Trade Commission dropped its appeal related to its proposed noncompete rule in 2025, reinforcing the reality that noncompetes are not a universal solution for protecting business information.
Meanwhile, remote work, personal devices, and cloud-based systems make it easy for information to move quickly, sometimes without clear evidence trails.
Artificial intelligence adds another layer. Analytical tools can rapidly extract patterns from data, making arguments about what is “readily ascertainable” more complex. Legal commentators, including Thompson Hine LLP, have noted that once proprietary information is widely disclosed or uploaded into external systems, secrecy claims become harder to defend.
Texas businesses also operate in a changing litigation environment. The Texas Business Court began hearing certain complex commercial disputes in 2025, potentially affecting how trade secret cases move procedurally.
The real question now is “Can we prove this information was secret and protected?”
What Courts Consider a Trade Secret
In plain English, a trade secret is information that:
- Has independent economic value because it is not generally known, and
- Is subject to reasonable efforts to keep it secret.
Most disputes turn on the second requirement. Businesses often focus on confidentiality language but overlook operational controls.
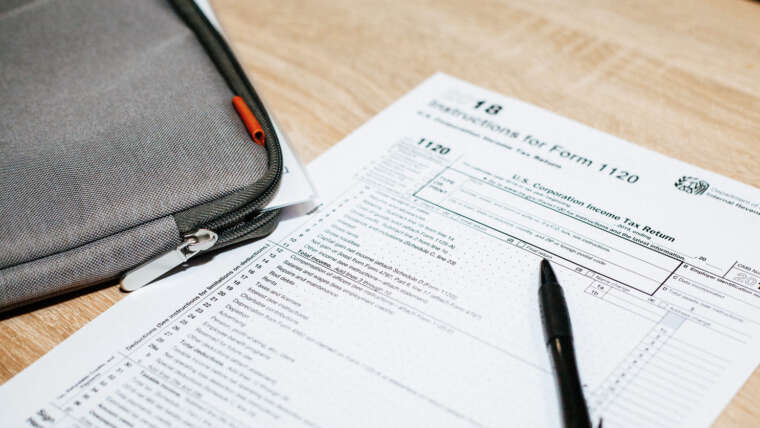
Trade secrets may be protected under state law and, in certain circumstances, under federal law as well. But regardless of legal framework, proof of active protection is the deciding factor.
Customer Lists: When They Are (and Aren’t) Protected

Customer lists are not automatically trade secrets. Protection depends on what the list actually contains and how it is handled.
Customer information is more likely to qualify when it includes:
- Decision-makers and relationship history
- Pricing sensitivity or contract terms
- Renewal timing and buying cycles
- Preferences, challenges, and internal notes
- Non-public contact pathways
Courts often view this broader category as customer intelligence, not just a list of names.
Protection weakens when information is:
- Publicly available or easily compiled
- Shared widely without restrictions
- Stored without labeling or access controls
- Exportable without tracking
If everyone in the company, or outside it, can access and share the information freely, secrecy becomes difficult to prove.
Pricing Information: A Frequent Source of Disputes
Pricing data is one of the most valuable and frequently contested categories of business information.
Protectable pricing information often includes:
- Bid formulas or cost models
- Discount thresholds and approval authority
- Margin strategies
- Bundling structures
- Renewal negotiation playbooks
Courts look closely at how pricing is handled operationally. Businesses weaken their position when pricing is casually distributed through unsecured emails or shared broadly without limitation.
Evidence that strengthens protection includes:
- Version-controlled pricing files
- Role-based access restrictions
- Written confidentiality policies
- Training acknowledgments
- Activity logs showing downloads or exports
Documentation often determines whether pricing information receives protection.
Protecting Business “Know-How”
Another critical category is proprietary know-how: internal processes that provide operational advantage.
Not everything an employee learns is protectable. General experience and skills travel with the employee. Specific, documented methods may not.
Examples that often qualify for protection include:
- Internal workflows and procedures
- Technical specifications or designs
- Sales scripts or decision frameworks
- Quality assurance protocols
- Vendor scoring systems
- Operational playbooks
A growing concern involves employees uploading internal processes into external AI tools. Once proprietary information is disclosed beyond controlled environments, secrecy arguments become significantly harder to sustain.
The Defensibility Checklist: Reasonable Measures That Work
Businesses strengthen trade secret protection by combining legal agreements, operational controls, and documentation.
Contracts and Policies
- Confidentiality and intellectual property agreements
- Clear definitions of protected information
- Return and deletion obligations upon departure
Training and Culture
- Annual confidentiality training
- Manager protocols for employee departures
- Clear expectations for handling business data
Technical Controls
- Role-based access permissions
- Monitoring for unusual downloads or transfers
- Secure storage and labeled repositories
- Automated offboarding procedures
Operational Discipline
- Separate sensitive information from routine materials
- Maintain a basic inventory of trade secrets
- Limit distribution to those who truly need access
Courts rarely require perfection. They look for consistency and intent.
The First 72 Hours After an Employee Leaves

Speed matters when protecting business information. A structured response improves both recovery and enforcement options.
Step 1: Contain Access
Adjust system permissions appropriately and preserve activity logs across email, cloud storage, and internal platforms.
Step 2: Identify What’s at Risk
Focus on specific information the employee accessed.
Step 3: Document and Communicate
Confirm return or deletion of company information. Use written communications that are factual and precise.
Step 4: Protect Customer Relationships Carefully
Internal messaging should be consistent and professional. External communications should avoid exaggeration or accusations.
Early discipline often determines whether escalation becomes necessary.
When Escalation Becomes Necessary
Some situations require legal intervention, particularly when evidence shows both acquisition and likely use of protected information.
Common indicators include:
- Unusual data downloads before departure
- Immediate customer solicitation
- Replication of proprietary pricing or processes
- Movement to a direct competitor
Potential remedies may include court orders restricting use or disclosure, expedited discovery, or negotiated resolutions. Venue strategy and timing can significantly influence outcomes.
Common Mistakes That Undermine Protection
Many trade secret claims fail due to avoidable internal practices:
- Labeling everything confidential but protecting nothing
- Failing to implement structured offboarding
- Delaying action after discovery
- Allowing unrestricted export of business data
- Making overly broad accusations instead of identifying specific information
Courts reward precision and preparation.
Your Next Steps Toward Stronger Trade Secret Defense
Trade secret protection in 2026 is not about reacting to employee departures, it is about building systems that make protection defensible before anyone leaves.
The strongest legal position combines preventive controls, documented practices, and rapid response.
When those pieces are in place, businesses are far better positioned to protect what gives them a competitive edge.If your company is looking to reinforce its safeguards, a smart first step is developing a clear trade secret inventory, strengthening confidentiality agreements, and formalizing a structured offboarding process. Proactive protection is always more cost-effective than reactive litigation. Reach out today to discuss how to build a more resilient trade secret strategy.